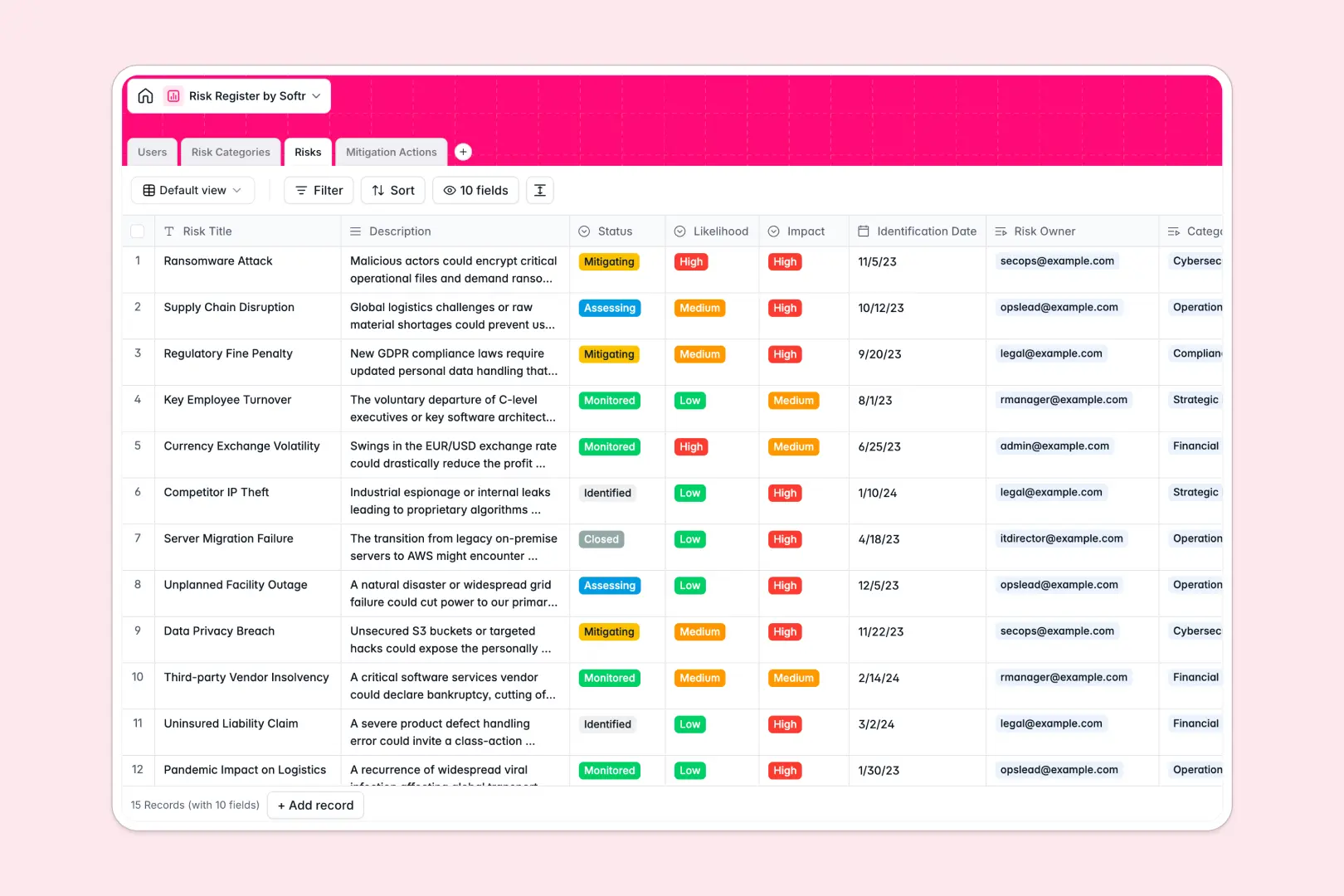
Your Risk Register database at a glance
Centralize your business vulnerabilities and mitigation efforts in one clear, structured view. This template gives risk managers immediate visibility into potential threats and their business impact.
Core Risks are categorized step-by-step and linked directly to Mitigation Actions and their assignees. This native structure ensures you always know who is handling a specific threat without jumping between tabs.
Built-in AI automatically drafts executive summaries for new threats and generates operational protocols for mitigation tasks. This saves your team hours of manual documentation.
Why managing business risks in spreadsheets breaks down
Tracking potential incidents across rigid spreadsheet rows quickly leads to lost action items, disconnected data, and critical delays.
What a structured database changes
When you relate risks to separate action and owner tables, updates happen instantly everywhere. You can easily link a mitigation task to a department without relying on broken spreadsheet formulas.
You never have to copy-paste assignee emails or cross-reference separate tabs for mitigation statuses. This is exactly what Softr Databases are designed for—keeping critical data clean and natively connected.
What you can do with this template
Quickly log vulnerabilities by impact and likelihood while instantly assigning mitigation actions to team members. Everything stays neatly grouped under standard business risk categories.
Using Database AI agents, your basic risk descriptions automatically transform into crisp executive summaries and actionable 5-step protocols. This keeps your team focused on rapid resolution rather than manual reporting.
-
Users
Manage risk owners and assignees with contact details and roles
-
Risk Categories
Classify organizational threats into standard business groupings
-
Risks
Log threats and use AI to generate executive summaries of each risk
-
Mitigation Actions
Track tasks and use AI to auto-draft operational protocols for risks
Who is this Risk Register database for
This ready-to-use system is designed for teams that need to identify and minimize business threats.
- Risk Managers: Identify, categorize, and prioritize threats based on clear impact and likelihood metrics.
- Department Heads: Supervise team-specific mitigation tasks and ensure operational protocols are followed.
- Compliance Officers: Maintain a clear, auditable trail of identified hazards and completed safety actions.
How to take it further
Easily rename select fields to match your company's specific hazard categories, impact levels, or likelihood scales. You can also add new columns to track financial exposure or localized regions.
Drag and drop your current risk logs into the system via CSV import for immediate value. You can also sync historical incident systems automatically via API.
When your operations scale, transform this secure data into a custom internal portal. A well-organized backend table ensures faster app deployment and a more reliable internal tool.
By configuring users and permissions, you guarantee that contributors only see the action items assigned to them, while admins maintain full oversight.
-
1
-
2
-
3
-
4
Frequently asked questions
-
What is a risk register database?
It is a structured system to centralize, track, and evaluate potential business threats. It helps organizations document vulnerabilities, assign ownership, and monitor mitigation actions to prevent costly incidents.
-
Why use a no-code database to build a risk management system?
A no-code database lets you deploy a production-ready tracking tool in minutes without any technical skills. It provides the rigid structure needed to manage hazards securely, giving your team the autonomy to adapt fields as new compliance requirements emerge.
-
How can AI help managing data for risk tracking?
AI heavily automates the documentation process when logging complex hazards. With built-in Database AI agents, the system follows precise prompts to automatically write executive summaries or generate 5-step protocols whenever a new risk is added.
-
Can I build an app with this risk register database?
Yes, using the interface builder, you can connect this backend to a custom frontend portal. Department heads can log in to view specific mitigation tasks, while security officers manage the entire portfolio based on secure access rules.
-
Is this Risk Register database free?
Yes, it is completely free to get started. Core database functionalities and unlimited collaborators are included in our free plan at no cost. Higher-tier plans offer increased database limits as your tracking needs grow.
Start building today. It's free!
Build and launch your first app in under 30 minutes.


