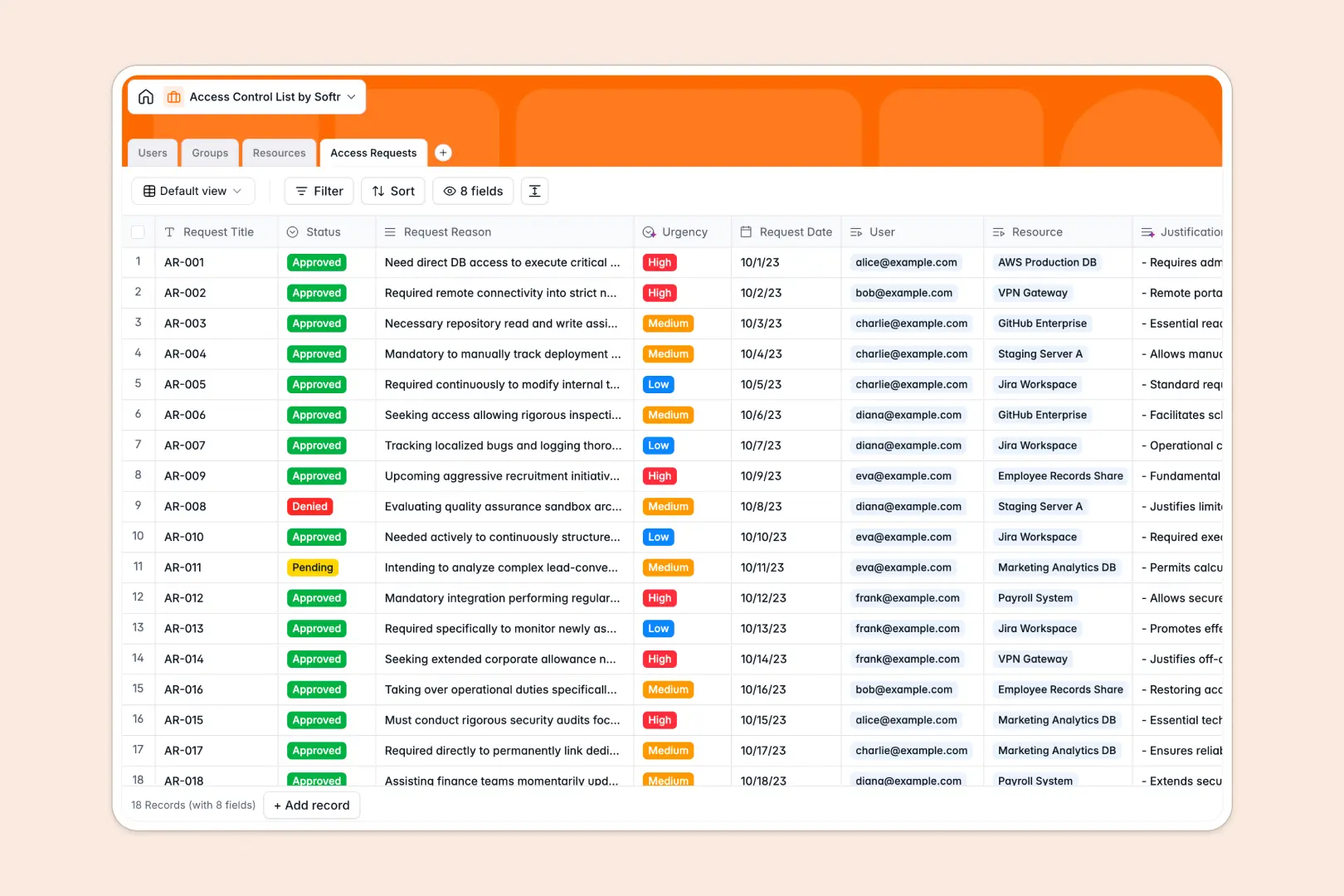
Your Access Control List database at a glance
This template centralizes your identity management so you can securely track exactly who has access to which systems. It eliminates the guesswork from IT security and compliance audits.
You can seamlessly connect specific Users and Groups directly to protected Resources like servers or databases. When someone needs new permissions, they simply submit an Access Request that links everything together.
Built-in AI automatically researches technical documentation for your resources and instantly classifies incoming requests by urgency. This means your IT team prioritizes critical approvals without reading through long justifications.
Why access control gets messy in Google Sheets
Tracking user permissions in a spreadsheet quickly becomes a massive security risk. As employees join, leave, or change roles, rows get accidentally deleted and it's impossible to see exactly who has access to a specific database.
What a structured database changes
A true system enforces strict rules so data stays clean and reliable. Instead of relying on fragile VLOOKUP formulas to connect a user to a server, records are natively linked.
This means you can assign an entire group to a high-security application with one click, without copy-pasting across rows. This is exactly what Softr Databases are designed for.
What you can do with this template
You can build a permanent, auditable log of every approved or denied permission request. Team leads can instantly see all resources assigned to specific users or groups in a single view.
Because it includes intelligent agent fields, the system dynamically scores the urgency of new requests based on the user's provided reasoning. It's a ready-to-use foundation that turns a manual IT chore into a self-maintaining process.
-
Users
Manage user identities, access levels, and roles with contact information
-
Groups
Organize users into clusters with AI Summaries of group organizational scale
-
Resources
Control protected assets using AI-powered technical documentation lookups
-
Access Requests
Track permissions history with AI-driven urgency and justification analysis
Who is this Access Control List database for
This template is designed for teams that need to secure their digital assets quickly without complex software.
- IT Managers: Quickly audit user permissions and revoke access when employees change roles.
- Security Teams: Maintain a clear, compliant log of access justifications and approvals for critical systems.
- Operations Leads: Automate the onboarding process by instantly assigning standard resource access to new hires.
How to take it further
You can easily tailor this system to fit your exact security policies. Add new resource types to the select fields or tweak the automated prompts to match your company's risk classification.
Stop starting from scratch by bringing your existing logs with you. Use a CSV upload or API sync to instantly import your current users, groups, and hardware inventory into the new tables.
When you are ready to stop managing requests manually, you can build an internal portal tailored to your team. Employees can log in to view their active access and submit new requests securely.
You have complete control over users and permissions, meaning standard team members only see their own requests. A well-structured backend makes building these secure internal tools incredibly easy.
-
1
-
2
-
3
-
4
Frequently asked questions
-
What is an access control list database?
It is a structured system that tightly tracks which users or groups are allowed to access specific digital or physical resources. It perfectly logs identity information, security levels, and formal permission requests in one reliable place.
-
Why use a no-code database to build an access management system?
Creating a custom IT management system usually takes months of costly development. A no-code database provides a production-ready, secure foundation instantly, allowing your IT team to maintain autonomy and adapt fields without writing scripts.
-
How can AI help managing data for access requests?
You get a powerful co-builder that helps configure your tables and filters using simple prompts. Additionally, Database AI agents act as automated assistants that analyze text, summarize long request justifications, and instantly classify request urgency without human intervention.
-
Can I build an app with this access control database?
Yes, you can easily turn this data into a secure employee portal using a dynamic interface builder. Staff can log in to submit requests while administrators review and approve them, with strict visibility rules ensuring everyone only sees what they should.
-
Is this Access Control List template free?
Yes, it is completely free to get started and copy into your workspace. Core databases are included on the free plan with unlimited collaborators. Higher-tier plans simply offer increased database limits as your organization grows.
-
How is this database different from Google Sheets?
Spreadsheets lack strict data types and native row relationships, making it incredibly easy to accidentally overwrite a critical server permission. As your company scales, navigating a dense grid of mixed data forms a massive compliance risk compared to a fully relational database system.
Start building today. It's free!
Build and launch your first app in under 30 minutes.


